In a previous tutorial here, I introduced you to the Linux firewall, iptables. iptables enables you create a custom firewall for your network quickly and easily without the cost of the commercial firewalls. In this tutorial, we will build upon iptables to create an application layer IDS/IPS by combining iptables with the malware detection rules of Snort.

Let’s introduce you to fwsnort. fwsnort translates Snort rules into iptables rules. fwsnort is written in Perl (Perl’s strong suit is its text processing capabilities) and attempts to cleanly translate Snort rules into iptables rules. Due to the complexity of many of the Snort rules, not all of them can be translated but as we will see, enough are translated to offer additional IDS/IPS capabilities to our iptables.
Snort and it’s simple text based rules are are capable of detecting and blocking a wide range of network and malware attacks. Many of the US military bases in the US rely entirely upon Snort to protect their networks. fwsnort enables us to take that network protection and alert system of Snort and build it into our inline iptables firewall to add an extra layer of detection to our network.
Although historically, firewalls and IDS/IPS have been distinctly different appliances, in recent years the line between these two has become blurred. Among some of the best and most expensive commercial firewalls, a hybrid firewall/IDS has become the norm.
A word of caution about IPS’s.
When using an IDS or Intrusion Detection System, it is expected that you will receive a significant number of false positives. It is up to the security analyst to separate the “wheat from the chaff” and decide whether an alert or log is an actual attack. With a IPS or Intrusion Prevention System, false positives can be much more problematic. A false positive will block the connection until the security analyst takes a positive action to remove it. This can lead to maintenance intensive tasks for the security analyst and possible frustration from the users.
Before starting, make certain that iptables and Snort are installed.
Step #1: Download and Install fwsnort
Let’s begin by installing fwsnort. It’s available in the Kali repository, so we can use the apt package management tool.
kali > sudo apt install fwsnort

Once you have it installed, let’s take a look at the help screen.
kali > sudo fwsnort -h

We can now install and translate the Snort rules from /etc/snort/rules by entering;
kali> sudo fwsnort -snort-rdir /etc/snort/rules

Note that these are the old rules that come pre-installed with your download of snort.

Now, to build the Snort rules into our iptables firewall, we need only run the script provided us at by fwsnort at /var/lib/fwsnort.
kali > ./fwsnort.sh
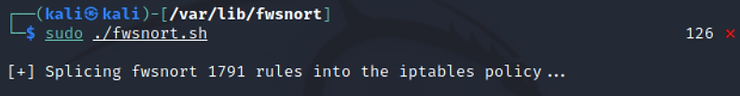
As you can see, 1791 rules have been spliced into our iptables. Now, when you run iptables, you will have the additional protection of nearly 1800 snort rules to block malware on your network!
Step #2 Installing and translating the Community Rules
New snort IDS rules are available at Snort.org and rather than having each group of rules in a file, Snort has placed all the files into a single file known as community.rules. To install these, we need to alter our command slightly. Instead of using the option snort-rdir for installing an entire directory of rules as we did above, now we use -snort-rfile option to import all the rules from the single file.
kali > sudo fwsnort -snort-rfile /etc/snort/rules/community-rules/community.rule

As you can see above, fwsnort was slightly less efficient at parsing and translating these rules for iptables. It successfully translated only 36%. Like above, to execute and install these rules into iptables, enter;
kali > ./fwsnort.sh
Step #3: fwsnort with Snort 3 rules
Recently, the good people at the Snort (Talos) division of Cisco (the owner of Snort) have developed a new version, Snort 3. With this new version, they have altered and streamlined the snort rule syntax. As a result, fwsnort is not able to translate these rules.
Let’s test fwsnort on these rule rules.
kali > sudo fwsnort -snort-rfile /etc/snort/rules/snort3-community-rules/snort3-community.rules

As you can see above, fwsnort was unable to parse and translate ANY of the snort 3 rules.
Summary
If you are looking for an free IPS for you network, consider fwsnort. Keep in mind that IPS’s can be problematic and can be high maintenance. When using snort rules, you best bet are the community rules preceding Snort 3.