Welcome back, my aspiring OSINT Investigators!
Often as OSINT investigators, pentesters and hackers, we need to determine if a email address of the target exits and, if so, whether it has been compromised. There are a multitude of locations where compromised emails and passwords are stored and not all of them contain all the latest dumps. Now we have a tool that can search through all of these databases and determine whether an email has been compromised and which data dump compromised it!
h8mail is a tool for finding compromised email addresses and their passwords from these data breaches. When you combine this tool with others such as TheHarvester or the crosslinked tool, you can harvest email addresses from an organization and then test to see if they have been compromised
Although there are numerous tools to do so, h8mail may be the best!

In this tutorial, we’ll examine how to use h8mail to quickly and effectively find an email in these data dump databases that may contain a current password or hash of the password.
Step #1: Install h8mail
The first step is to install h8mail. The developer has made this process simple and painless. We can simply download it from pip3.
kali > pip3 install h8mail

If you have not yet installed pip3, you can do so by entering;
kali > apt install python3-pip
Step #2: h8mail help
Before get started, let’s look at this tool’s help screen. When I installed it, the package placed my binary file in /home/kali/.local/bin. Yours may be different. If this directory is not in your $PATH variable, you will need to add it or simply navigate to the directory where the binary is located.
kali > cd /home/kali/.local/bin
Now, if we preface the command with the name of the interpreter (python3), we should be able to run this script. Simply append a -h after the command to display the help file.
kali > python3 h8mail -h

This tool has a multitude of options, but in its simplest form its usage syntax looks like this:
python3 h8mail -t <target email address>
Step #3: Acquire and Install API Keys
Next, we need to create a configuration file and provide API keys to the databases we want to search. To create a configuration file, enter;
kali >python3 h8mail -g
h8mail will now create config file in the directory you executed this command from. I ran the command from /home/kali/.local/bin, so my config file was placed in that directory. Yours may be different, but h8mail will display the directory and file name after creating the file as seen below.

Now, you have the option to use API keys from the premium services such as haveibeenpwned.com. To do so, click on the API tab at the top of the screen and it will open screen like that below. haveibeenpwned.com is among the largest repositories of data dumps on the web. They require that you first provide a password and verify that password. Finally, they ask that you pay a nominal $3.50/month to use their service

Now that you have an API key, open the configuration file and place the API key in the config file.
kali> mousepad /home/kali/.local/bin/h8mail_config.ini

I have placed my API key after the hibp (haveibeenpwned) line and uncommented it and the leak-lookup_pub line.
Now you are ready to begin your search!
Step #4: Search for email addresses in dumps
h8mail’s syntax is rather simple for simple searches. We only need to use the -t option followed by the target email address to search the dumps for this email followed by the -c option and the location of your config file, such as;
kali > python3 ./h8mail -t linda.vu@gmail.com -c /home/kali/.local/bin/h8mail_config.ini

When we hit enter, h8mail begins its search through the databases we specified in the configuration file.
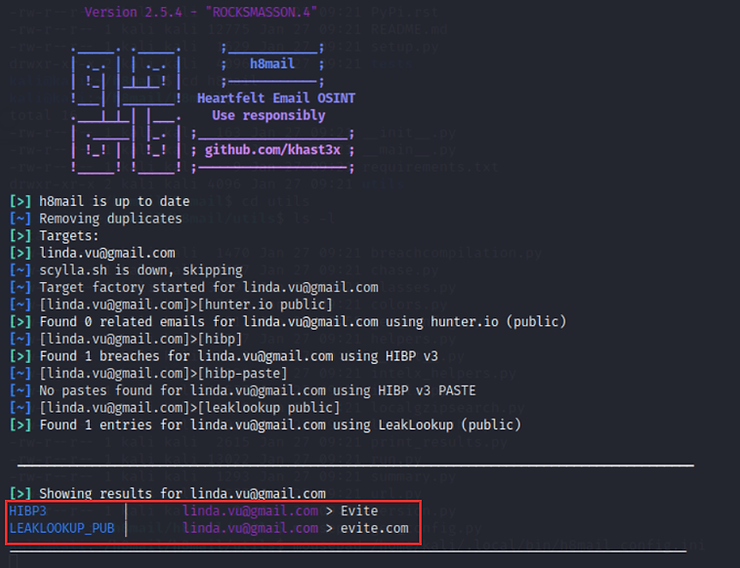
As you can see above, h8mail found this email in both HIPB3 and LEAKLOOKUP_PUB databases as part of the evite.com data dump.
If we want to save the results in a text file, we can use the -o option followed the name of file we want the results saved to.
kali > python3 ./h8mail -t linda.vu@gmail.com -c /home/kali/.local/bin/h8mail_config.ini -o linda_results.txt

To open the output file, you can use any text editor or the less command to view the output.

Summary
Very often, as OSINT investigators or pentesters we need to know whether an email has been compromised in the numerous data dumps that occur almost daily. H8mail is an excellent, out-of-the-box tool for automating the search through the dump databases. In addition, h8mail can read from a .txt file and output to a .csv file when working with large data sets making your OSINT investigation faster and more efficient.